Businesses in the U.S. and across the globe are under attack. State and city governments are, too. The enemy is invisible and so are its weapons. But the attacker’s power to wreak havoc, cause deep financial losses and exploit formerly secure information is highly visible.
These attacks are of the cyber nature, and their numbers are growing. According to UK-based Juniper Research, the global cost of data breaches is predicted to rise from $3 trillion each year to over $5 trillion by 2024. That’s an average annual growth of 11% and one that’s primarily driven by increasing fines for data breaches as global and regional regulations tighten.
Cybersecurity breaks out of IT
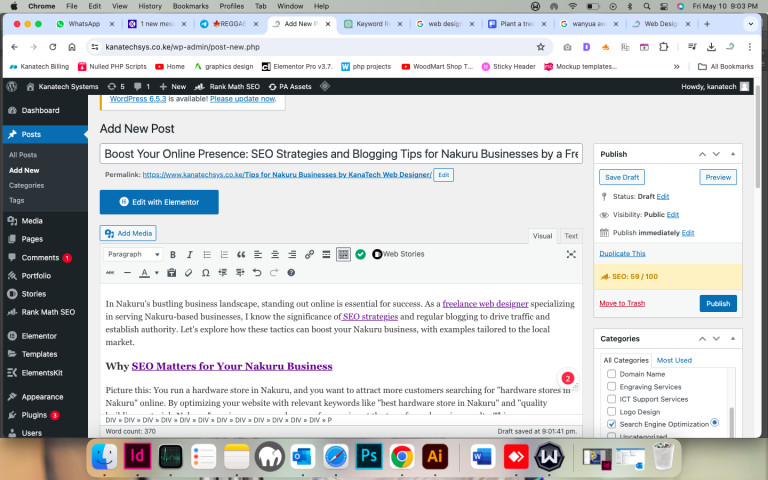
Chengcheng Li is an associate professor at the University of Cincinnati’s School of Information Technology. He works with students in the university’s online Master of Science in Information Technology (MSIT) program.
“There’s a huge demand for more people in the workforce who are focused on cybersecurity,” says Li. “It’s an area of concern for every business today — financial sectors, service businesses, small- and large-sized companies. That’s why our MSIT program curriculum includes dedicated cybersecurity courses in principles of cybersecurity and security forensics and other courses that are closely related to cybersecurity, such as IT Infrastructure, system administration, internet of things and data mining.”
Li says that, in the past, cybersecurity wasn’t a separate focus area in IT. Cybersecurity tasks were performed by a mix of professionals from the networking, system and database administration, programming and data analytics areas. But many companies now require information technologists who are dedicated to cybersecurity and the organizational structure to support that focus area, as well.
Cybersecurity-focused roles
For people who already work in IT but choose to refocus their energies in the area of cybersecurity, the switch can be lucrative.
Job-market analytics company Burning Glass Technologies has been tracking the cybersecurity job market since 2013. In its June 2019 report, it states that the number of cybersecurity job postings has grown 94% since 2013, compared to only 30% for IT positions overall. This growth is three times faster than the overall IT market.
Burning Glass’s research shows that cybersecurity jobs account for 13% of all IT jobs. On average, however, cybersecurity jobs take 20% longer to fill than other IT jobs and pay 16% more. This works out to an average of $12,700 more per year.
According to the U.S. Bureau of Labor Statistics, the average salary for an information security analyst is $98,350. Analysts plan and carry out security measures to protect an organization’s computer networks and systems. “Their responsibilities continually expand as the number of cyberattacks increases,” Li says.
National Security Agency partnership
The University of Cincinnati is one of only a few institutions in the country to have National Security Agency (NSA)-sponsored National Centers of Academic Excellence in both cyber defense and cyber operations.
Li says the University’s School of Information Technology received several grants from the NSA, National Science Foundation and Ohio state government to support its cybersecurity education program.
The University of Cincinnati is also now home to the Ohio Cyber Range, a virtual environment where participants can learn about cybersecurity and practice defending networks against threats of all kinds.
“We know cybersecurity is a growing field that offers vast job opportunities,” says Li. “We value our NSA connection, offer curriculum that’s aligned with them and encourage our students to attend NSA-sponsored career fairs, too.”
Students who apply to join the University’s online MSIT program live in or outside the U.S. Most complete the program part-time while working full-time. Students can complete the program in three semesters if they choose to go full-time, but the typical student completes the program part-time in about two years.
Cybersecurity and security forensics studies
Two courses in the MSIT curriculum focus solely on cybersecurity: Principles of Cybersecurity and Enterprise Security and Forensics.
The cybersecurity course introduces students to the field by discussing the evolution of information security into cybersecurity, cybersecurity theory and the relationship of cybersecurity to nations, businesses, society and people.
Students are exposed to multiple technologies, processes and procedures. “They learn how to analyze and report on the threats, vulnerabilities and risks and develop strategies to mitigate those problems,” says Li.
In the enterprise security and forensics course, MSIT students learn network forensics fundamentals and strategies to design and implement systems that provide protection while still focusing on the needs of those systems’ user communities. Li adds that the course explores network forensic analysis tools that better prepare students for the challenges they may face in the workplace.
Security concerns not slowing down
With our global dependency on faster technologies, cloud storage and more “things” being connected to the internet of things, businesses and governments worldwide won’t take their foot off the information security brake anytime soon. They’ll be required to spend more time, money and energy battling hackers, monitoring potential data breaches and fixing systems that are too easy to attack.
“It’s easy to believe we’re in a scary, vulnerable time,” says Li, “but I’d rather focus on the fact it’s an exciting time for IT professionals and continue our work to equip the next generation of leaders in this field.”